Stop Crypto Scams Before They Hit Your Customers

Cryptocurrency fraud is evolving faster than traditional financial crime, creating new challenges for risk management teams. Directors of Fraud Prevention, Fraud Detection Managers, and other specialists must identify and prevent sophisticated crypto scams targeting both customers and organizational operations. From pig butchering schemes to fake DeFi protocols, understanding how crypto scams work is essential to safeguard assets, maintain regulatory compliance, and protect your organization’s reputation.
Understanding Crypto Scams
Crypto scams are a significant and growing threat. Risk teams need to recognize the patterns and tactics scammers use to exploit businesses and individuals.
Common crypto scams include:
- Romance scams that trick victims into transferring crypto to fraudulent wallets.
- Fake investment platforms promising high returns through ICOs or DeFi tokens.
- Phishing attacks and business email compromise (BEC) aimed at redirecting crypto payments.
Types of crypto scams span Ponzi or pig butchering schemes, wallet takeovers, deepfake identity fraud, and cross-chain transaction exploits.
How crypto scams work: Scammers exploit trust, technical ignorance, and the pseudonymous nature of crypto networks to move assets out of victims’ wallets, often making recovery nearly impossible.
Technology Detection Methods
Advanced technology is key to identifying crypto scams before they cause major damage.
- Wallet clustering analysis: Identifies wallets linked to suspicious activity patterns.
- Blockchain transaction tracing: Tracks abnormal transaction paths and cross-chain activity.
- AI-based pattern recognition: Detects behavioral patterns in scams, including pig butchering and fake DeFi protocols.
- Blockchain analytics integration: Enables real-time monitoring of high-risk addresses and unusual transaction volumes.
These methods provide actionable insights, allowing teams to intervene before fraudulent transfers succeed.
Compliance Workflow Integration
| Compliance Challenge | Description |
| Wallet Ownership Verification | Ensures that users are the legitimate owners of the wallets they connect. |
| Source of Crypto Funds Verification | Confirms that incoming assets are not derived from illicit activity. |
| Sanctions Screening | Cross-checks wallet addresses against known illicit entities. |
| On/Off-Ramp Monitoring | Tracks crypto transactions entering or leaving the platform to detect suspicious activity. |
| Regulatory Alignment | Integrates AML/KYC compliance measures while minimizing customer friction. |
By embedding these measures into existing workflows, organizations can maintain compliance, reduce operational risk, and detect crypto fraud proactively
Team Training & Response
Fraud teams must be equipped to recognize and respond to crypto scams quickly. Recognizing red flags, such as unusual wallet activity, high-pressure requests for crypto transfers, or inconsistent identity documentation, is critical. Institutions need to be aware of typologies like BEC targeting crypto payments, fake ICOs or DeFi projects, and social engineering scams. Clear response protocols for escalating suspicious activity, freezing transactions, and coordinating with blockchain analytics platforms are essential. Continuous education ensures that teams remain vigilant and up to date on emerging crypto scams.
Operational Impact Analysis
The consequences of crypto scams are substantial. Financially, stolen crypto is often irrecoverable, leading to direct losses. Regulatory scrutiny is heightened when AML/KYC processes fail, potentially resulting in fines and reputational damage. Fraud incidents also increase customer acquisition and retention costs, as trust erodes and onboarding expenses rise. Publicized crypto fraud cases can severely impact brand credibility, highlighting the importance of proactive monitoring, detection, and prevention strategies.
Solution Comparison Framework
Selecting the right tools is essential for preventing crypto fraud effectively. Blockchain analytics platforms offer transaction tracing and wallet risk scoring, while crypto compliance solutions automate KYC verification, sanctions checks, and real-time monitoring. Real-time transaction monitoring flags high-risk crypto movements before they succeed, and integration with existing fraud systems ensures operational continuity while enhancing protection. The right combination of solutions reduces false positives, improves detection accuracy, and strengthens overall fraud prevention workflows.
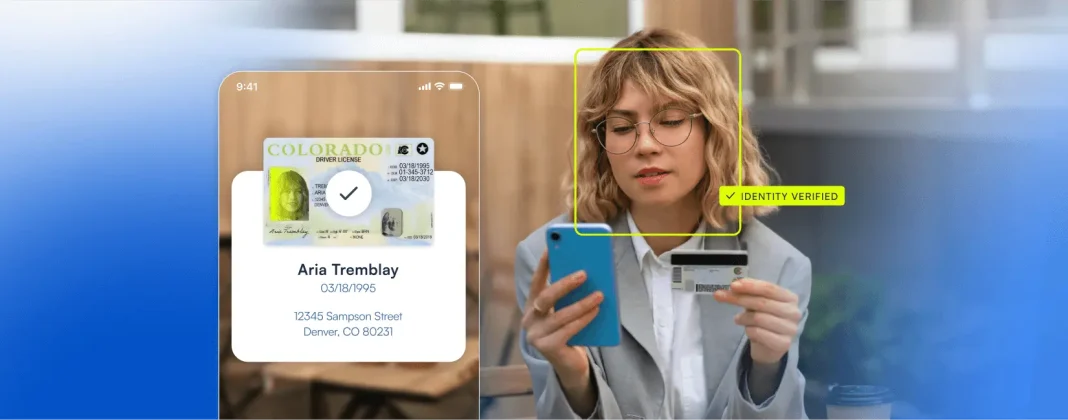
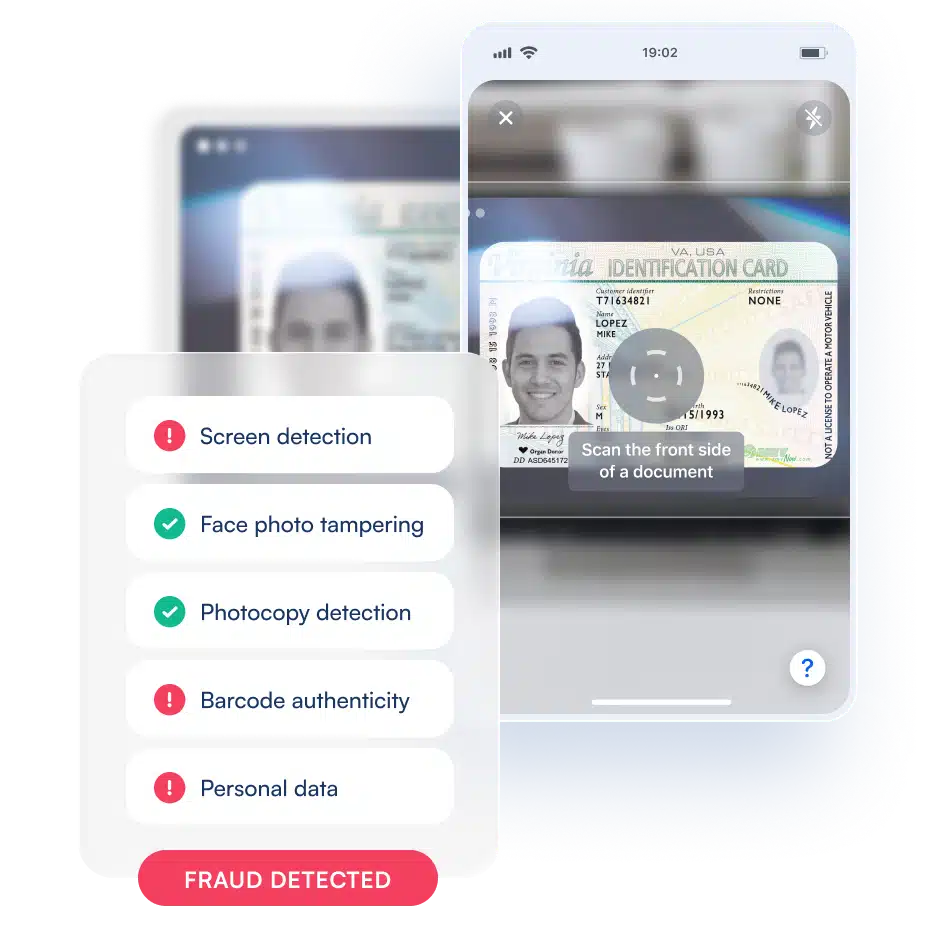
How Microblink Helps Prevent Crypto Scams
Microblink’s identity verification platform enables businesses to detect and prevent crypto scams through advanced biometric and document checks. Its AI-driven technology identifies patterns such as fake investment schemes and social engineering attacks. Integration-ready solutions support KYC/AML compliance and real-time monitoring of crypto on/off ramps. Microblink reduces false positives and streamlines customer onboarding while verifying wallet ownership, source-of-funds, and sanctions screening. Risk teams can proactively prevent fraud, safeguard assets, and maintain regulatory compliance with confidence. Get in touch today to learn more.