2026 Fraud Trends Report: Staying Ahead of Attacks
Fraud trends are no longer incremental shifts that risk teams can address with small rule updates or periodic reviews. They are structural changes driven by automation, generative AI, and organized fraud networks that operate faster than manual controls can respond. For risk management leaders, understanding how fraud is evolving is now inseparable from maintaining regulatory compliance, protecting customer trust, and keeping onboarding conversion rates intact.
Across industries, fraud is moving earlier in the customer lifecycle, targeting identity creation rather than transaction abuse alone. The result is a growing gap between traditional fraud controls and the threats they are meant to stop.
How Fraud Trends Are Changing
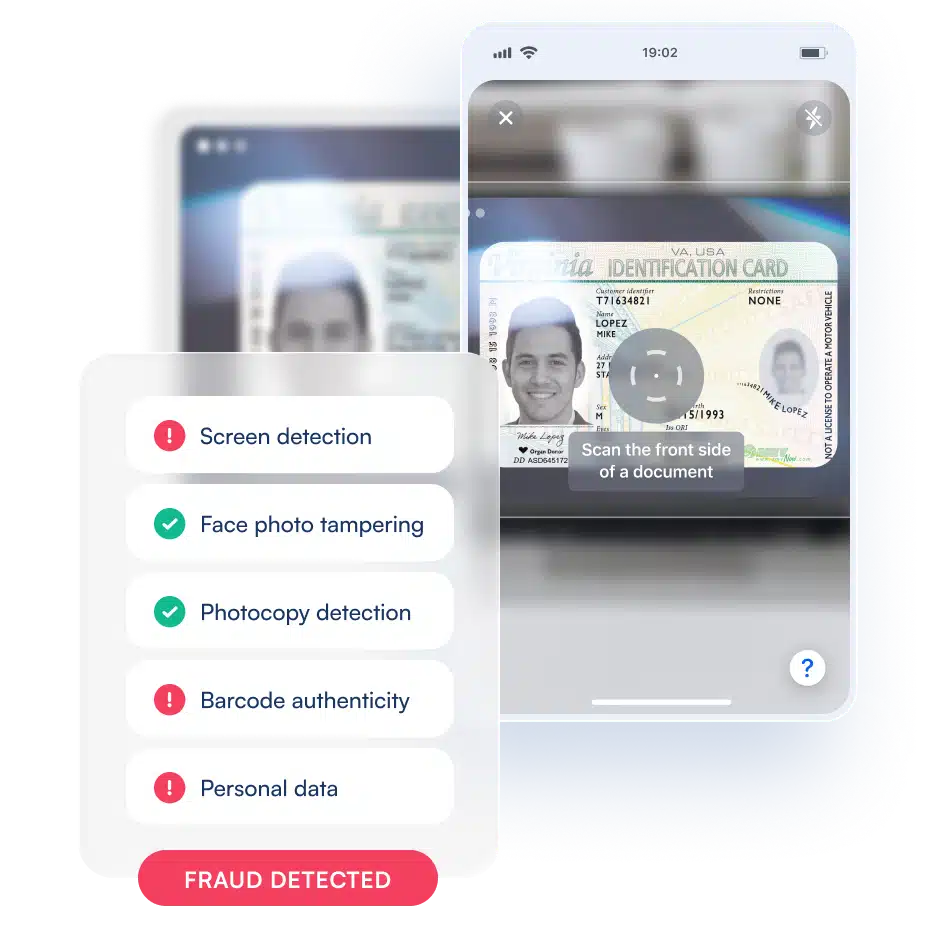
Modern fraud increasingly exploits weaknesses in identity verification rather than payments infrastructure. Synthetic identity fraud blends real and fabricated data to create identities that pass basic checks, age quietly, and then scale abuse over time. At the same time, deepfake-enabled impersonation is no longer experimental. It is being actively deployed against selfie checks, liveness detection, and document capture workflows that were not designed to operate under adversarial AI pressure.
Account takeover remains a major threat, but it is increasingly downstream of identity compromise. When fraudsters can reliably create or purchase verified-looking identities, they gain long-term access rather than needing to repeatedly breach accounts. This shift makes prevention at onboarding and early lifecycle stages significantly more valuable than post-transaction controls.
For regulated businesses, these fraud trends introduce a second-order risk. Identity failures that lead to fraud exposure often surface later as KYC and AML audit findings, where regulators examine not only outcomes but the adequacy of controls themselves.
Common Fraud Types Businesses Face Today
- Synthetic identity fraud using blended real and fabricated identity attributes
- AI-generated document fraud, including altered and fully synthetic IDs
- Deepfake-assisted impersonation targeting selfie and liveness checks
- Account takeover driven by compromised or fraudulently created identities
- Friendly fraud and chargeback abuse tied to weak identity-to-payment binding
Why Traditional Controls Are Falling Behind
Many fraud programs still rely on static rules, point-in-time checks, and manual review processes designed for a different threat landscape. These approaches struggle in three critical ways.
First, manual review does not scale. As fraud attempts increase in volume and sophistication, review queues become bottlenecks that slow onboarding and increase operational costs. Second, static verification creates blind spots. A one-time identity check cannot account for behavioral drift, credential reuse, or identity reuse across channels. Third, overly conservative rules raise false rejection rates, turning legitimate customers away while still failing to stop advanced fraud.
The consequence is a familiar but costly pattern: fraud loss rises, audit risk increases, and customer experience degrades simultaneously.
Quantitative Benchmarks Risk Teams Should Track
| Metric | Industry Reality | What High-Performing Programs Target |
|---|---|---|
| False rejection rate | 5–10% common in regulated onboarding | <2% with risk-based flows |
| Manual review rate | 20–40% in legacy programs | <5% with automation |
| Average onboarding time | 3–7 minutes | Under 60 seconds |
| Cost per verification | Increases with review volume | Declines with scale |
| Fraud detection latency | Post-transaction discovery | Pre-transaction prevention |
Reducing False Rejections Without Increasing Risk
One of the most damaging side effects of outdated fraud controls is the rejection of legitimate customers. High false positive rates erode brand trust, suppress growth, and often push customers toward less regulated competitors. Reducing false rejections requires moving away from binary pass-or-fail decisions and toward adaptive, risk-based verification.
Smart retry flows, progressive verification, and contextual risk assessment allow low-risk users to pass quickly while escalating only genuinely suspicious cases. This approach improves both security and conversion because it aligns verification effort with actual risk rather than applying uniform friction.
What Effective Fraud Prevention Looks Like Today
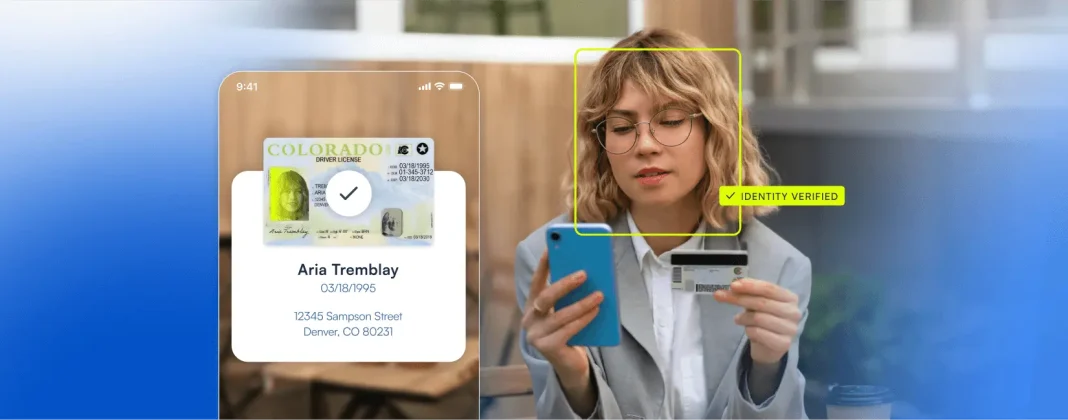
Modern fraud prevention programs are built on continuous identity assessment rather than isolated checks. They combine document intelligence, biometric signals, device context, and behavioral analysis into a unified decisioning layer that operates across onboarding and transactions. Machine learning models continuously adapt to new fraud patterns, while automation minimizes reliance on manual review.
Critically, effective programs treat identity as a lifecycle concern. The same signals used to verify a user at onboarding and new account creation inform future risk decisions, enabling earlier detection and faster response without reintroducing friction.
Turning Fraud Trends Into a Competitive Advantage
Fraud trends will continue to evolve, but the organizations that respond effectively share common traits. They invest in automated identity intelligence, design verification flows around real risk rather than assumptions, and align fraud prevention with customer experience rather than treating them as opposing forces.
Microblink supports this approach by providing automated, high-accuracy identity verification that helps businesses stay ahead of emerging fraud trends while meeting KYC and AML requirements at scale. By reducing manual review, lowering false rejections, and enabling faster onboarding, modern identity intelligence transforms fraud prevention from a defensive cost center into an operational advantage.