Top AI Solutions for Identity Threat Intelligence

In the modern cybersecurity landscape, the traditional « castle-and-moat » defense strategy has effectively collapsed. As digital perimeters dissolve into distributed workforces and cloud-native architectures, identity has become the primary attack surface for the enterprise. This shift has necessitated a move away from static network security toward dynamic Identity Threat Detection and Response (ITDR) and AI-driven verification frameworks.
Today’s security leaders are facing a dual-front war: preventing sophisticated fraud at the point of entry and detecting compromised credentials that have already bypassed the perimeter. The most resilient organizations are now integrating AI-powered digital onboarding—capable of sniffing out deepfakes and synthetic identities in milliseconds—with continuous behavioral monitoring to halt lateral movement in real-time.
This guide analyzes the top-tier software solutions leveraging artificial intelligence to secure the entire identity lifecycle. Whether you are looking to streamline KYC compliance with frictionless onboarding or harden your Active Directory against credential theft, these tools provide the automation and intelligence required to maintain a robust Zero Trust posture.
Comparison Table: Top Identity Threat Intelligence Providers
| Product | Compliance Features | Industry Focus | AI Capabilities | User Experience | Developer Experience |
|---|---|---|---|---|---|
| Microblink | KYC/AML Compliance, Age Verification | Financial Services, E-commerce | AI-Powered Document Verification, Liveness Detection | Fast onboarding, On-device processing | Requires SDK integration, Developer resources needed |
| CrowdStrike Falcon Identity | FIDO2-compliant MFA, Real-time Threat Detection | Enterprise Security, Hybrid Environments | Real-time Traffic Analysis, Unified Agent Architecture | Seamless for existing CrowdStrike users | Unified agent, No new sensors required |
| Microsoft Defender for Identity | Native M365 Integration, Automatic Attack Disruption | Microsoft-centric Enterprises | UEBA & Anomaly Detection | Deep Microsoft ecosystem integration | Complex configuration, E5 licensing for full features |
| Silverfort | Agentless MFA, Unified Identity Protection | Legacy Systems, Hybrid Environments | Real-time Policy Enforcement | Agentless platform, Protects legacy assets | Complex initial integration, Proxy-based architecture |
| Stellar Cyber Open XDR | ITDR Embedded in XDR, Automated Threat Response | Mid-market Security Teams | Multi-Layer AI Correlation | Unified dashboard, Reduces alert fatigue | Open integration ecosystem, Learning curve |
| SentinelOne Singularity | Deception Technology, Endpoint-first Architecture | Threat Hunting, Endpoint Protection | Ranger AD Assessment, AI-driven Analysis | Integrated deception technology, Proactive defense | Requires SentinelOne agent, Endpoint-focused |
This chart offers a quick overview of the strengths and focus areas of each product, helping users to understand which solution might best fit their needs based on compliance features, industry focus, AI capabilities, user experience, and developer experience.
1. Microblink

Platform Summary:
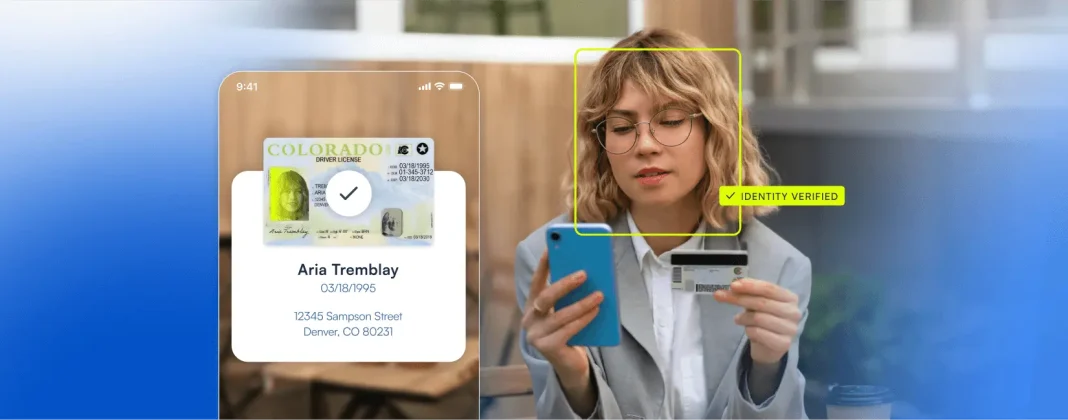
Microblink provides a sophisticated identity verification layer designed to stop fraud at the very first touchpoint: digital onboarding. By utilizing advanced AI models that run directly on the user’s device, the platform ensures that identity documents are authentic and that the person presenting them is physically present. This approach not only hardens security but also drastically improves the user experience by removing the friction typically associated with manual verification. For Fraud Decision-Makers, Microblink represents a proactive shift in identity security—ensuring only legitimate, verified users enter the ecosystem, while also addressing critical privacy concerns for enterprises operating under strict regulatory frameworks like GDPR or CCPA.
Key Benefits
- Stops synthetic identity and deepfake fraud at the source, before it enters your ecosystem.
- On-device AI processing enhances privacy and reduces regulatory risk.
- Lightning-fast onboarding improves user conversion and reduces abandonment.
- Seamless integration as a core component in broader threat intelligence platforms.
Core Features
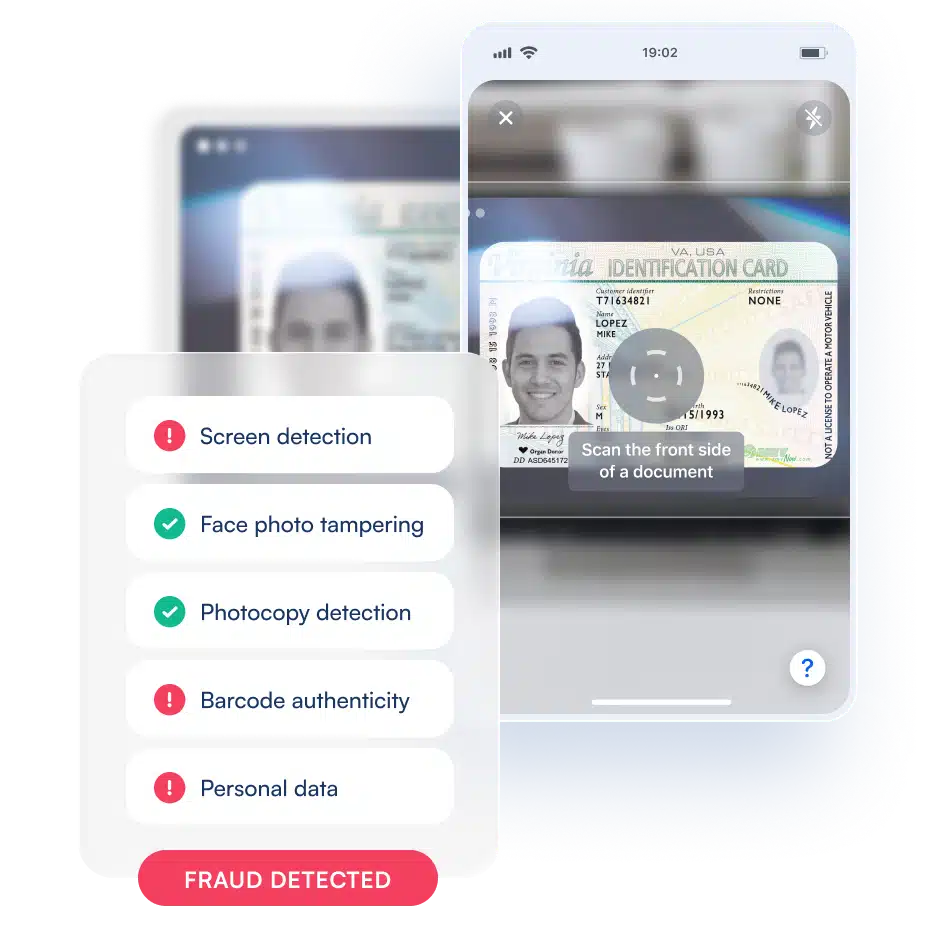
- AI-Powered Document Verification: Multi-layered analysis checks for digital tampering, screen presentation attacks, photocopies, and data consistency between VIZ and MRZ, supporting over 2,500 document types globally.
- Advanced Biometric and Liveness Detection: Certified liveness detection defends against deepfakes and face swaps, ensuring the user is real and physically present.
- High-Speed, On-Device Processing: SDKs engineered for performance, capturing and extracting ID data in under a second, with much of the processing happening directly on the user’s device.
- Customizable Risk Workflows: Tailor risk scoring, set custom thresholds, and configure workflows to match your platform’s logic and your clients’ risk appetite.
Primary Use Cases
- Bolstering Identity Verification Platforms: Integrate as the core document and biometric verification component within broader threat intelligence platforms.
- Preventing Synthetic Identity Fraud at Onboarding: Multi-layered checks as the first line of defense in digital onboarding workflows.
- Mitigating Account Takeover (ATO) and Payment Fraud: Re-verify users during high-risk activities to combat ATO and card-not-present fraud.
Recent Updates
- Expanded support for Arabic script OCR.
- Improved deepfake detection capabilities within the liveness module.
- Enhanced global document coverage and unified user experience.
Limitations
- Primary focus is on verification and onboarding, requiring integration with other tools for continuous post-login monitoring.
- Requires integration of SDKs into mobile or web applications, demanding developer resources for initial setup.
2. CrowdStrike Falcon Identity

Platform Summary:
CrowdStrike Falcon Identity is a cloud-native solution that integrates identity protection directly into the endpoint security stack. By analyzing authentication traffic in real-time, it identifies anomalies that suggest credential theft or lateral movement. Its single-agent architecture provides a frictionless way for existing customers to gain deep visibility into identity-based threats, correlating device health with user behavior for robust conditional access enforcement.
Core Features
- Real-time Traffic Analysis of authentication events for immediate threat detection.
- FalconID MFA: FIDO2-compliant, phishing-resistant multi-factor authentication.
- Unified Agent Architecture: No additional sensors needed for existing Falcon users.
Primary Use Cases
- Credential Theft Detection and blocking of infostealer-harvested credentials.
- Lateral Movement Prevention through real-time conditional access policies.
- Hybrid Identity Monitoring across on-premises AD and cloud-based Entra ID.
Recent Updates
- Introduction of Falcon Privileged Access for automated privilege management.
- Enhanced identity-driven case management for streamlined incident response.
Limitations
- Most effective for organizations already using the CrowdStrike Falcon endpoint platform.
- Less comprehensive visibility into non-Windows assets and third-party identity stores.
3. Microsoft Defender for Identity
Platform Summary:
Microsoft Defender for Identity is a cloud-based security solution leveraging on-premises Active Directory signals to identify, detect, and investigate advanced threats. Natively integrated into the Microsoft 365 Defender portal, it provides a unified investigation experience across identities, endpoints, and applications—making it essential for Microsoft-centric enterprises.
Core Features
- Native M365 Integration for seamless visibility across on-premises AD and Entra ID.
- UEBA & Anomaly Detection to identify sophisticated attacks with high accuracy.
- Automatic Attack Disruption to disable compromised accounts or force password resets.
Primary Use Cases
- Securing Hybrid AD Environments by bridging legacy and modern identity landscapes.
- Privilege Escalation Detection for sensitive group changes and suspicious privileged activity.
- SOC Automation via integration with Microsoft Defender XDR.
Recent Updates
- Tighter integration with the broader Defender XDR suite.
- Enhanced cross-domain visibility and improved identity security posture management.
Limitations
- Weaker coverage for non-Microsoft identity stores and third-party SaaS applications.
- Advanced features often require the top-tier E5 licensing package.
4. Silverfort

Platform Summary:
Silverfort offers a unique, agentless approach to identity protection by monitoring authentication requests at the directory level. It enforces security policies and MFA across all resources—including legacy applications and command-line interfaces—without requiring software deployment on every server, making it ideal for organizations with significant technical debt.
Core Features
- Agentless Platform integrating directly with IAM directories.
- MFA for Legacy Applications and resources that don’t natively support modern authentication.
- Unified Identity Protection across AD, Entra ID, Okta, and Ping Identity.
Primary Use Cases
- Protecting Legacy Systems and infrastructure that cannot support modern protocols.
- Service Account Monitoring for highly privileged machine-to-machine access.
- Lateral Movement Protection by enforcing step-up authentication for sensitive resources.
Recent Updates
- Expanded integrations for deeper support of cloud identity providers.
- Enhanced real-time policy enforcement for non-standard protocols.
Limitations
- Slight latency in high-volume environments due to authentication traffic analysis.
- Initial integration with domain controllers and identity providers can be complex.
5. Stellar Cyber Open XDR

Platform Summary:
Stellar Cyber Open XDR is a comprehensive security operations platform that includes ITDR as a core feature. It correlates identity data with signals from the network, cloud, and endpoints, providing a holistic view of the attack surface. Its open approach is particularly well-suited for mid-market security teams looking to consolidate multiple security functions.
Core Features
- Embedded ITDR directly within the Open XDR platform.
- Multi-Layer AI Correlation for high-fidelity alerting.
- Open Integration Ecosystem for ingesting data from any security tool.
Primary Use Cases
- Mid-Market SOC Operations for visibility without managing multiple point solutions.
- Insider Threat Detection by baselining user behavior and flagging anomalies.
- Automated Threat Response, such as disabling users in AD upon high-severity alerts.
Recent Updates
- Improved AI-driven alert scoring.
- Expanded API connectors for seamless identity telemetry ingestion.
Limitations
- May lack granular identity management features found in specialized PAM or IGA tools.
- Learning curve for teams seeking only simple identity monitoring.
6. SentinelOne Singularity Identity

Platform Summary:
SentinelOne Singularity Identity focuses on protecting Active Directory and endpoints with integrated deception technology. By planting fake credentials and decoy assets, it proactively detects attackers the moment they attempt credential harvesting, while also providing continuous assessment of AD hygiene.
Core Features
- Deception Technology with decoy credentials and honeypots.
- Endpoint-First Architecture to detect credential theft techniques at the source.
- Ranger AD Assessment for continuous AD hygiene monitoring.
Primary Use Cases
- Detecting Active Directory Attacks such as Kerberoasting and Golden Ticket.
- Stopping Infostealers targeting browser-stored passwords and session cookies.
- Threat Hunting with detailed endpoint and identity telemetry.
Recent Updates
- Deeper integration of identity telemetry into the Singularity Data Lake.
- Enhanced cross-product correlation and investigation speeds.
Limitations
- Less comprehensive visibility into cloud-native identity stores and SaaS applications.
- Deception features require careful planning and configuration.
Looking for more on how to integrate robust identity verification into your risk stack?
Explore Microblink’s developer resources or see how AI-powered onboarding can transform your fraud prevention workflow.
For further reading, see our guides on KYC compliance automation and AI in fraud prevention.
Frequently Asked Questions
What is identity threat intelligence, and why is it important for fraud prevention?
Identity threat intelligence refers to the collection, analysis, and application of data related to identity-based threats—such as credential theft, account takeover, and synthetic identity fraud. It is crucial for fraud prevention because attackers increasingly target user identities as the primary vector for breaching organizations. By leveraging threat intelligence, businesses can proactively detect suspicious behaviors, prevent unauthorized access, and respond quickly to emerging threats, thereby reducing the risk of financial loss and reputational damage.
How does AI improve digital onboarding and identity verification processes?
AI enhances digital onboarding and identity verification by automating the analysis of identity documents, detecting deepfakes, and verifying liveness in real-time. Advanced AI models can quickly identify fraudulent documents, spot inconsistencies, and confirm that a real person is present during onboarding. This not only increases accuracy and reduces manual review workloads but also streamlines the user experience—leading to faster onboarding, higher conversion rates, and stronger compliance with KYC/AML regulations.
What are the main differences between agent-based and agentless identity security solutions?
Agent-based solutions require software to be installed on endpoints or servers, providing deep visibility and control over those devices. They are often preferred for environments where endpoint security is critical. Agentless solutions, on the other hand, integrate directly with identity directories and monitor authentication traffic without deploying software to individual assets. This makes them ideal for protecting legacy systems, cloud resources, and environments where installing agents is impractical. The choice depends on your infrastructure, compliance needs, and risk appetite.
How can organizations protect against synthetic identity and deepfake fraud during onboarding?
Organizations can defend against synthetic identity and deepfake fraud by implementing multi-layered AI verification tools that analyze both the authenticity of documents and the liveness of users. Features such as advanced OCR, biometric matching, and certified liveness detection help ensure that only genuine users are onboarded. Additionally, integrating customizable risk workflows and continuous monitoring can further reduce the risk of fraudulent accounts entering the ecosystem.
What should Fraud Decision-Makers consider when choosing an identity threat intelligence provider?
Fraud Decision-Makers should evaluate providers based on several factors: compliance features (KYC/AML support, privacy regulations), AI capabilities (accuracy, speed, deepfake detection), integration complexity, coverage across legacy and cloud systems, user and developer experience, and scalability. It’s also important to consider the provider’s ability to integrate with existing security stacks, support for global document types, and the level of automation available for threat detection and response.