Agent to Agent Protocol: Secure Identity Verification Communication Standards

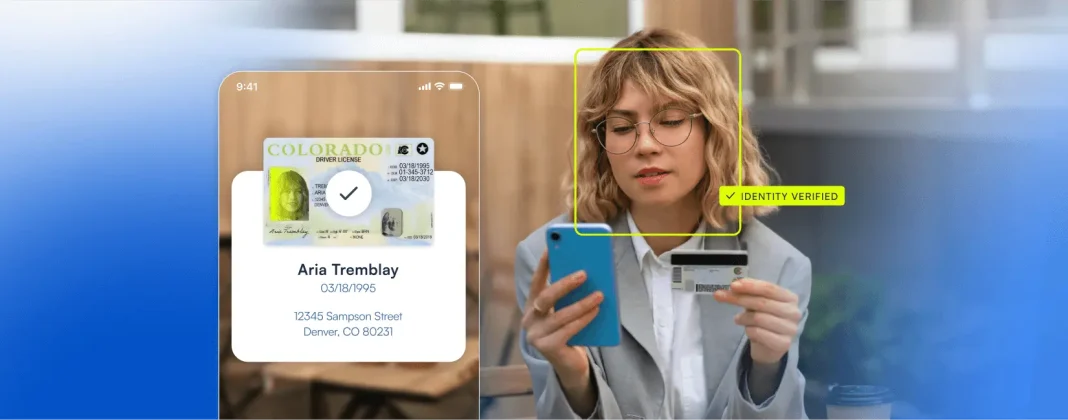
An agent-to-agent protocol, often shortened to A2A protocol, defines how autonomous systems securely communicate, exchange identity signals, and coordinate decisions without human intervention. In identity verification and KYC workflows, this protocol acts as the connective tissue between internal verification engines and external agents such as fraud services, document validation providers, biometric engines, or regulatory systems.
For VP-level engineering leaders and solution architects, the purpose of an agent-to-agent protocol is straightforward: enable secure, interoperable, and auditable communication across identity systems while maintaining strict control over trust boundaries, data exposure, and compliance obligations.
Why agent-to-agent protocols matter in modern KYC architectures
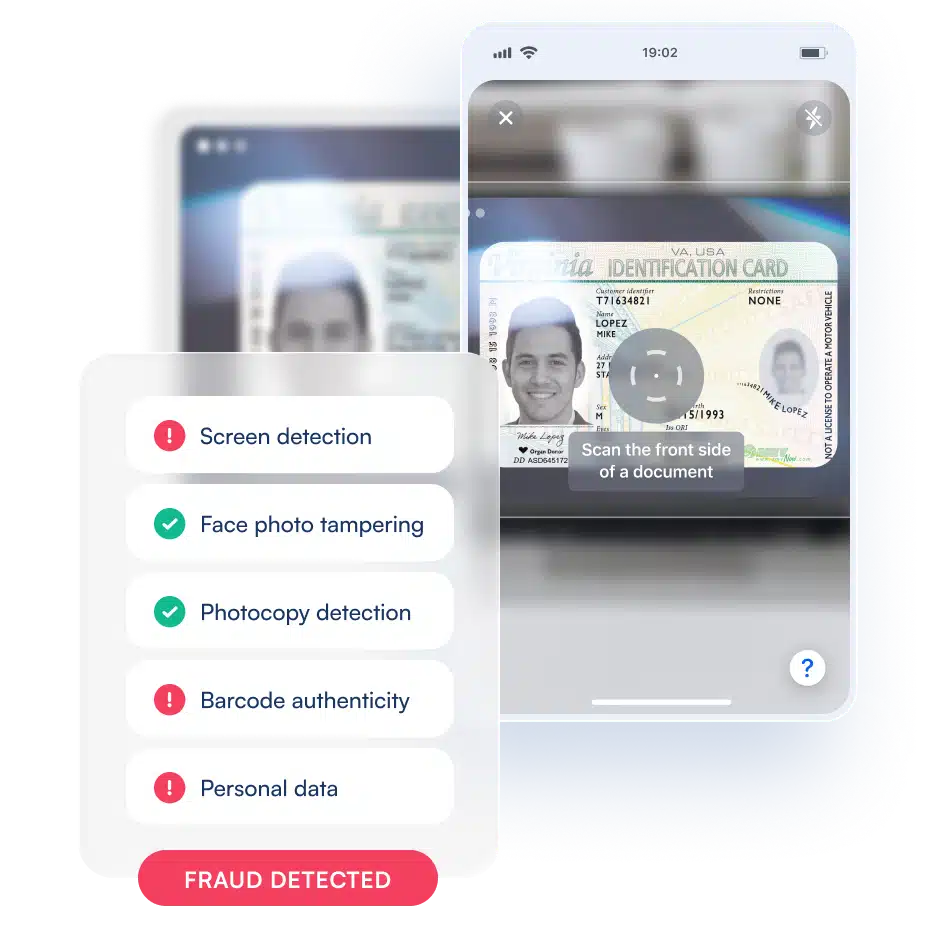
Traditional identity verification stacks were designed as tightly coupled systems. They assume static integrations, rigid workflows, and limited external coordination. That model breaks down quickly when organizations need to detect synthetic identities and AI-powered fraud, adapt risk scoring in real time, or comply with evolving KYC and AML requirements across jurisdictions.
An A2A protocol introduces a standardized communication layer that allows verification agents to discover each other, authenticate trust, and exchange verified identity assertions without exposing raw personal data unnecessarily. This design directly addresses the need for faster onboarding, stronger fraud detection, and defensible compliance postures.
Core capabilities of an agent-to-agent protocol
- Agent discovery and trust establishment
Verification agents identify one another and establish cryptographic trust before any identity data is exchanged. - Secure message exchange
Identity signals, risk scores, and verification results are transmitted using authenticated, encrypted channels. - Interoperability across vendors and systems
Internal platforms and third-party services communicate using standardized schemas rather than custom integrations. - Auditability and traceability
Every verification decision and data exchange can be logged, creating a defensible audit trail for AML reviews. - Policy-driven data sharing
Agents exchange only the minimum data required, supporting privacy-by-design principles.
Agent-to-agent protocol workflow in identity verification
| Stage | What Happens | Why It Matters |
|---|---|---|
| Discovery | Verification agents identify compatible counterparts and supported capabilities | Prevents brittle, hard-coded integrations |
| Authentication | Mutual authentication establishes cryptographic trust | Blocks unauthorized agents and spoofed services |
| Secure Messaging | Agents exchange identity assertions, risk signals, or decisions | Reduces exposure of raw PII |
| Decision Coordination | Signals are combined to determine verification outcomes | Improves accuracy and fraud detection |
| Audit Logging | Events are recorded for compliance and review | Supports KYC and AML audit requirements |
Security, privacy, and compliance by design
A properly implemented A2A protocol is security-first by necessity. Identity systems are high-value targets, and any protocol used to connect them must assume hostile environments. Authentication mechanisms ensure only trusted agents participate, while secure messaging protects identity data in transit.
From a compliance perspective, agent-to-agent protocols simplify regulatory alignment. Instead of moving sensitive customer data between systems, agents can exchange verification proofs and risk outcomes. This reduces data residency issues, limits breach impact, and supports regulatory expectations around data minimization and transparency.
Integration scenarios and real-world benefits
Agent-to-agent protocols are particularly effective in regulated industries where identity verification must balance speed, accuracy, and compliance. Banks use A2A communication to accelerate KYC onboarding while layering in synthetic identity fraud detection. Fintech platforms rely on it to orchestrate multiple verification services without degrading user experience. Compliance teams benefit from clear, machine-readable audit trails that simplify AML reporting and regulatory exams.
Microblink applies these principles by enabling secure, efficient communication between verification components within a single architecture. This approach allows organizations to modernize legacy systems, integrate third-party agents, and scale identity verification workflows without sacrificing security, accuracy, or cost performance.
In practice, an agent-to-agent protocol is not just a technical abstraction. It is the foundation that allows identity systems to operate at modern scale while meeting the demands of fraud prevention, regulatory compliance, and customer trust.