KYC Procedure Best Practices & Implementation

Here, we’ll explore the significance of KYC regulations in various sectors and dig into a crucial question: when should the KYC procedure be performed?
What you need to know about KYC
KYC serves as a foundational practice to verify customer identities, adhering to legal and regulatory standards. Understanding this intimately is a crucial first step—starting with important legal requirements.
Legal and regulatory requirements
The KYC procedure is more than best practice. It’s a legal imperative for financial institutions. KYC compliance procedures involve stringent measures, with financial entities mandated to establish a customer identification program (CIP), among other things. This program ensures the collection of essential customer information, including name, date of birth, address, and identification number.
Components of effective KYC procedures
A strong KYC procedure isn’t just about checking a name and ID. It’s about fully understanding who your customer is and monitoring for changes over time.
Here are the key parts of an effective KYC verification procedure:
- Customer Identification Program (CIP): Collects key details like name, address, date of birth, and ID number.
- Customer Due Diligence (CDD): Classifies risk based on the info gathered and checks if customer behavior matches expectations.
- Ongoing Monitoring: Regularly checks for unusual activity, updates in customer info, or changes in sanctions lists.
- Risk Assessment: Adjusts how often reviews happen based on the customer’s risk level.
Together, these elements create a KYC compliance procedure that adapts to changing risks and regulations—not just at onboarding but throughout the customer relationship.
Industries requiring KYC
The legal imperative for KYC procedures extends across diverse sectors, each with its unique challenges and obligations. Some industries that require proper KYC compliance procedures include the following:
Financial institutions
Financial institutions play a pivotal role in upholding KYC obligations and are often on the front lines in the fight against illicit financial activity. This includes:
Financial institutions play a pivotal role in upholding KYC verification procedures and are often on the front lines in the fight against illicit financial activity. This includes:
| Institution | KYC Responsibilities |
| Banks | Conduct identity verification, monitor transactions, perform customer due diligence (CDD), and report suspicious activity. |
| Credit Unions | Verify member identities, maintain compliance records, assess account activity for anomalies, and adhere to AML regulations. |
| Investment Firms | Evaluate client risk tolerance, verify investor accreditation, and monitor for unusual investment patterns. |
| Insurance Companies | Perform KYC on policyholders and beneficiaries, screen for politically exposed persons (PEPs), and assess risk for high-value policies. |
| Brokerage Firms | Verify trader identities, ensure transparency in account creation, and detect unusual trading activity. |
| Fintech Companies | Use digital KYC (eKYC) for onboarding, apply biometric or AI-based identity checks, and monitor digital transactions. |
| Money Service Businesses (MSBs) | Verify sender/receiver identities, monitor wire transfers and remittances, and report large cash transactions. |
| Lending Institutions | Authenticate borrower identities, verify income sources, and assess credit and fraud risk during loan issuance. |
| Cryptocurrency Exchanges | Enforce KYC during account creation, verify wallets, track blockchain activity, and report suspicious crypto transactions. |
Online platforms
Online platforms have emerged as dynamic hubs in the digital age, requiring robust KYC mechanisms to combat evolving threats. Key players in this domain include:
| Platform Type | KYC Responsibilities |
| Cryptocurrency Exchanges | Enforce identity verification, screen for money laundering risks, monitor wallet activity, and report suspicious transactions. |
| Social Media Networks | Verify user identities for financial features (e.g., monetization, advertising), detect fraudulent activity, and protect account integrity. |
| Gaming Platforms | Confirm player identities, prevent underage access, monitor in-game transactions for suspicious activity, and enforce responsible gaming policies. |
| Online Gambling Sites | Validate user identity and age, monitor betting behavior, and ensure compliance with local AML and KYC laws. |
| E-commerce Marketplaces | Verify vendor and buyer identities, assess transaction legitimacy, and flag suspicious purchases or sales. |
| Peer-to-Peer (P2P) Platforms | Confirm participant identities, secure payment channels, and detect patterns of fraud or illicit transfers. |
| Crowdfunding Platforms | Authenticate campaign organizers and donors, ensure funding legitimacy, and prevent misuse of raised funds. |
| Streaming Services with Monetization | Verify content creator identities, ensure lawful fund disbursement, and monitor monetization transactions for compliance. |
Trigger events for KYC
KYC acts as the first line of defense against money laundering and financial crime. Timing is critical to preempt potential risks and ensure the integrity of financial transactions. Here are some of the key events that should start the KYC procedure

Account-Related Triggers
Initiating a new account always necessitates KYC verification. Some other account-related triggers include
- Account reactivation after dormancy: Dormant accounts that are reactivated should go through renewed KYC checks to validate current information.
- Product or service upgrades: When a customer upgrades to a higher-risk product, new KYC verification procedures should ensure suitability and compliance.
- Multiple account relationships: Customers with multiple accounts may present higher complexity or risk, warranting an additional review.
Transaction-Related Triggers
- Large or high-value transactions: When transaction values exceed set thresholds, enhanced KYC compliance procedures are typically required to assess legitimacy.
- Cash-intensive transactions: High volumes of cash activity may indicate risk and should trigger detailed KYC reviews.
- Cross-border transactions: Transfers across jurisdictions, especially into or out of high-risk countries, necessitate stronger scrutiny.
- Transaction pattern changes: Sudden or unusual changes in behavior may indicate suspicious activity and should prompt an updated KYC procedure.
- Unusual activity or transaction behavior: Outliers from a customer’s normal patterns often signal risk and require a closer look.
Risk and Compliance Alerts
- Suspicious activity detection: If flagged by internal systems or third parties, suspicious activity should immediately trigger a new KYC verification procedure.
- Sanction list matches: Customers who appear on global sanction or watch lists must undergo rapid investigation and appropriate KYC actions.
- High-risk jurisdiction involvement: Activity involving countries with weak AML enforcement or known corruption issues requires enhanced KYC scrutiny.
- Third-party risk alerts: External data providers may flag risk signals that prompt deeper due diligence.
- Enhanced due diligence triggers: When risk thresholds are breached, enhanced due diligence protocols—such as source-of-funds checks—must be activated.
- PEP (Politically Exposed Person) identification: Customers identified as PEPs must be assessed more rigorously due to their heightened risk exposure.
- Customer complaint investigations: A formal complaint can uncover previously unknown issues, prompting a recheck of customer identity and risk.
- Internal audit findings: Audit discoveries related to gaps or anomalies may require targeted KYC compliance procedures.
Customer Data Updates
- Changes to personal or business information: Updates like a new address, name, or ownership status should trigger a refresh of the customer profile.
- Updates in ownership structure (for businesses): Material changes in company ownership or control require reassessment of beneficial ownership.
- Change in customer risk rating: If a customer moves from low to medium or high risk, the KYC profile must be revisited and updated.
- Customer status change (e.g., becomes a PEP): A shift in the customer’s political or legal standing can drastically alter risk posture and KYC requirements.
Understanding the trigger events for KYC verification processes is pivotal in fortifying the financial landscape, proactively addressing risks, and ensuring robust compliance across diverse financial domains. Trigger events, in other words, are the answer to “when?” in KYC.
Customer communication strategies during KYC
Clear, transparent communication is essential to building trust during the KYC procedure. Customers may not always understand why they’re being asked to provide certain documents or undergo identity verification steps, especially if they’ve already interacted with your platform. That’s why it’s important to clearly explain the purpose of KYC and how it helps protect both the customer and the business from fraud and financial crime. Messaging should emphasize security, compliance, and ease of use—reassuring users that the steps are standard, secure, and part of a regulated environment.
Just as important is how you deliver that message. Communication should be timely, consistent, and available across multiple channels—from onboarding emails and in-app messages to FAQs and live support. If a customer is flagged for additional verification, proactive messaging can reduce friction and prevent drop-off. This is especially critical in digital environments, where users expect seamless experiences. A well-crafted communication strategy not only supports a smoother KYC verification procedure, but also strengthens the customer relationship at a moment when trust matters most.
How automation can help you stay compliant
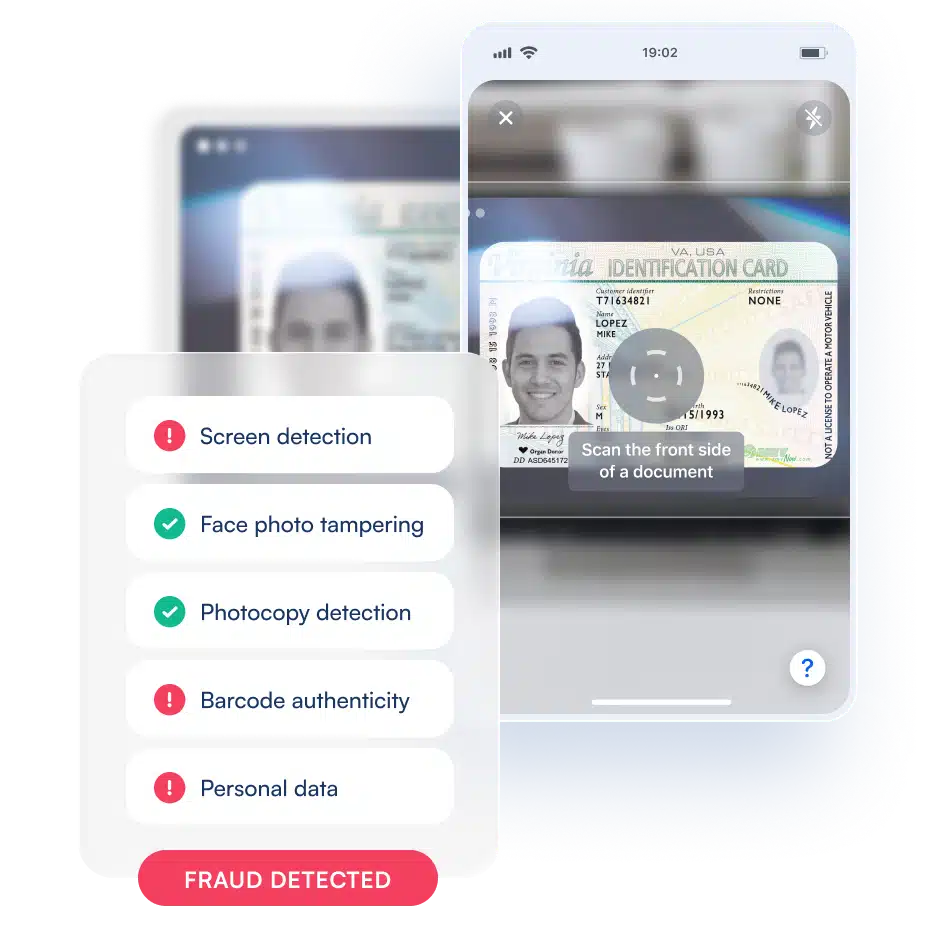
Staying compliant with KYC regulations can be resource-intensive, especially amid an evolving regulatory landscape. However, technological advancements offer a lifeline, notably in AI and blockchain.
Embracing AI-driven KYC verification procedures expedites processes like verifying a customer’s identity, customer due diligence, enhanced due diligence, risk assessment, and verification of KYC documents. Automation can also ensure real-time scrutiny of financial transactions with ongoing monitoring, promptly detecting and addressing any anomalies. This kind of per-transaction scrutiny is crucial for compliance with AML (anti-money laundering) regulations and for preventing fraud.

Efficient KYC solutions powered by automated systems and the right expert partner can not only streamline your KYC compliance procedures but also fortify customer identity security. Leveraging automation isn’t just about modernization—it’s becoming necessary to keep the KYC procedure realistic, balancing strict security with usability and customer satisfaction.
Prioritizing KYC excellence
The importance of KYC in any financial setting cannot be overstated. This fundamental practice, spanning customer identification, due diligence, and ongoing monitoring, is a regulatory requirement and a safeguard against financial crimes. To get it right requires the right timing, and automation is key there.
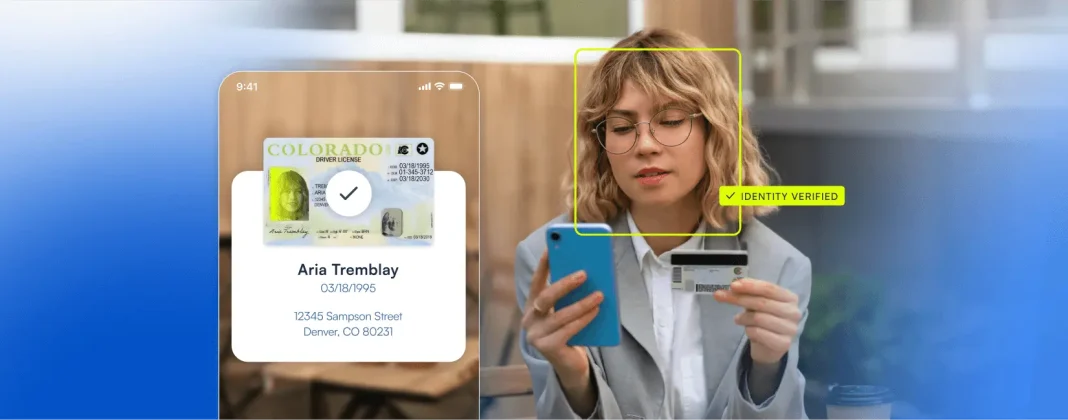
How Microblink can help
Enter Microblink with their document verification superpowers. We help organizations get the KYC procedure timing right with AI-powered technology built by people. That way, you know you’re in compliance regarding business relationships, building trust in customer relationships, and staying efficient everywhere else.
To learn more about how Microblink can help with your end-to-end KYC, get in touch.