User Authentication API: Secure, Scalable Identity Verification for Modern Applications

As digital products scale and fraud grows more sophisticated, user authentication APIs have become a critical layer of application security. For software engineers and solution architects, the challenge is no longer just confirming that a user can log in, but ensuring the person behind the screen is real, trustworthy, and compliant with regulatory requirements. A modern API user authentication strategy must balance security, speed, developer experience, and fraud resilience without introducing friction that drives users away.
This guide breaks down how user authentication APIs work, what features matter most, how they integrate into existing systems, and why traditional approaches are no longer enough on their own.
What Is a User Authentication API?
A user authentication API is a software interface that allows applications to verify user identities and control access to protected resources. At its most basic level, it confirms that a user is who they claim to be before granting access. In more advanced implementations, it evaluates identity signals, behavioral patterns, and fraud indicators to continuously assess risk throughout the user lifecycle.
Authentication APIs typically sit between frontend applications and backend services, handling identity checks, token issuance, session validation, and access control. For teams operating in regulated industries or high-risk environments, authentication increasingly overlaps with identity verification, fraud prevention, and compliance workflows.
Core Authentication Methods Used in APIs
Most authentication APIs rely on a small set of well-established mechanisms. Each serves different use cases and security needs, and many systems combine multiple methods.
| Authentication Method | How It Works | Strengths | Limitations |
|---|---|---|---|
| Basic Authentication | Username and password sent with each request | Simple to implement | Insecure without HTTPS, vulnerable to credential theft |
| API Keys | Static keys identify applications or users | Easy for server-to-server auth | Poor user-level security, hard to rotate safely |
| OAuth 2.0 | Delegated authorization using access tokens | Widely adopted, flexible | Complex to implement correctly |
| JWT (JSON Web Tokens) | Signed tokens carry identity claims | Stateless, scalable | Token leakage can be dangerous |
| OpenID Connect (OIDC) | Identity layer on top of OAuth 2.0 | Strong user authentication standard | Requires careful configuration |
While these methods form the foundation of API user authentication, they primarily answer the question “Can this user access the system?” rather than “Is this a legitimate user?”
Why Traditional Authentication Alone Is No Longer Enough
Credential-based authentication methods are increasingly vulnerable to modern fraud tactics. Stolen credentials, account takeovers, and synthetic identities can bypass standard login flows without raising immediate red flags. Even strong token-based approaches cannot detect whether an identity itself is fabricated or manipulated.
This gap is especially risky during remote onboarding, high-value transactions, or regulated workflows that require identity assurance. Fraudsters now use generative AI to create convincing fake documents, faces, and personas that pass basic checks but fail under deeper scrutiny.
Key Features of a Modern User Authentication API
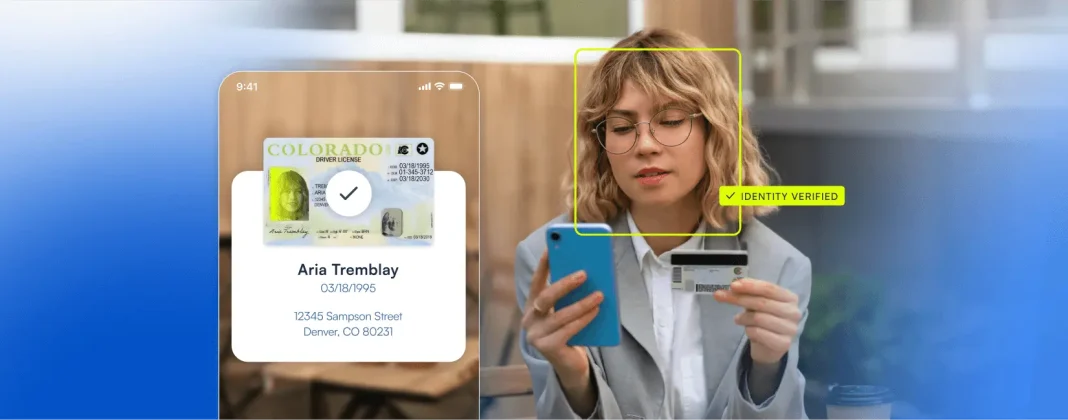
A modern user authentication API must go beyond login credentials to evaluate identity integrity and risk contextually. Advanced APIs incorporate multiple layers of verification, including government-issued ID validation, biometric matching, device intelligence, and behavioral analysis.
Real-time risk scoring allows the system to adapt authentication requirements dynamically. Low-risk users move through frictionless flows, while high-risk signals trigger step-up authentication such as biometric checks or document verification. This adaptive approach improves both security and user experience.
Equally important is auditability. APIs should provide detailed logs, decision explanations, and reporting to support KYC, AML, and internal security reviews without requiring custom tooling.
Preventing Identity Fraud With Authentication APIs
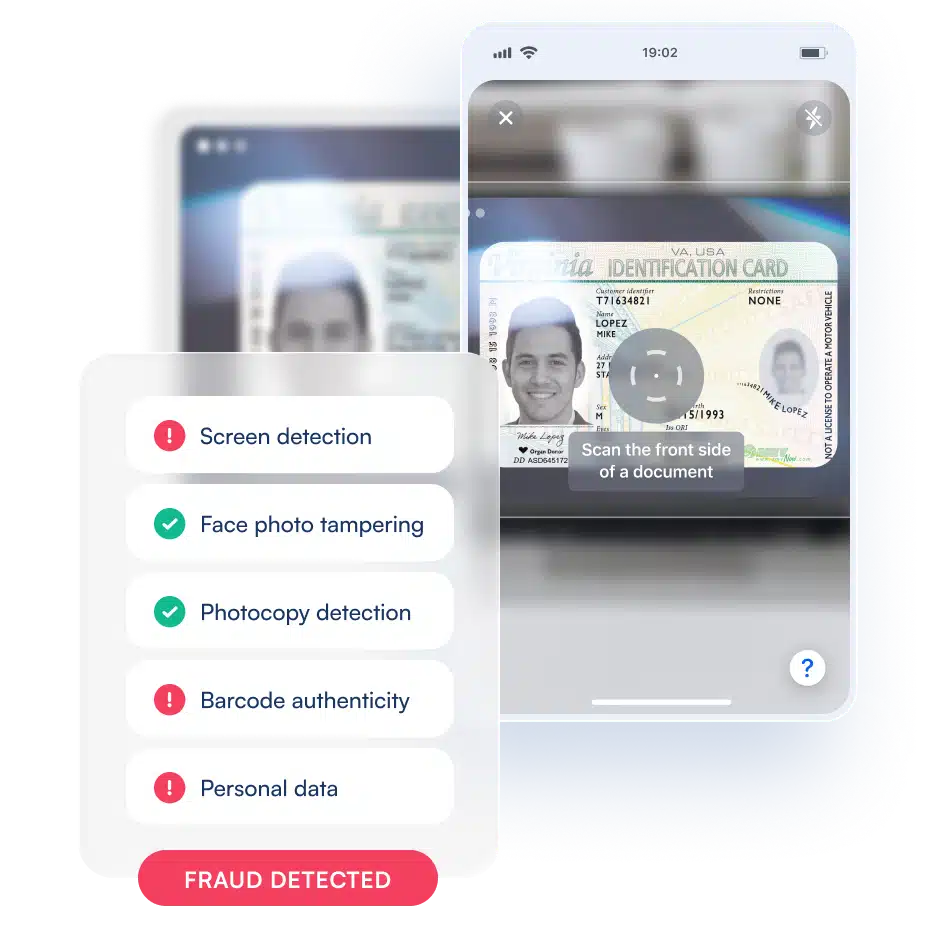
Authentication APIs play a crucial role in preventing identity fraud when they integrate fraud signals directly into the decision-making process. Rather than treating authentication as a one-time gate, advanced systems continuously assess identity confidence across sessions and actions.
By combining document verification, face biometrics, and AI-based fraud detection, APIs can identify synthetic identities, deepfake attempts, and replay attacks that bypass traditional controls. This layered approach significantly reduces false positives while catching sophisticated fraud patterns early.
Integrating a User Authentication API Into Existing Systems
For engineers and architects, integration effort matters. A well-designed authentication API should fit naturally into existing application infrastructure, whether monolithic or microservices-based. RESTful endpoints, clear SDKs, and strong documentation reduce implementation time and risk.
Authentication APIs should support common identity providers, work alongside existing OAuth or OIDC setups, and allow gradual rollout. This enables teams to enhance security without rewriting authentication logic or disrupting production systems.
Handling High-Risk and Non-Traditional Authentication Scenarios
Many competitors overlook edge cases that matter in real-world deployments. Remote onboarding, for example, introduces higher fraud risk due to the lack of physical presence. In these scenarios, biometric verification and document authenticity checks become critical fallback mechanisms.
Similarly, device-based authentication can add an additional layer of trust by linking users to known devices and detecting anomalies when behavior changes unexpectedly. APIs that support flexible workflow customization allow teams to tailor authentication flows based on geography, user segment, or transaction risk.
Authentication in Low-Connectivity or Offline Environments
Not all authentication happens under perfect network conditions. In emerging markets or mobile-heavy use cases, low connectivity can disrupt real-time verification. Advanced authentication APIs address this with offline token generation, delayed credential validation, and secure synchronization once connectivity is restored.
These capabilities ensure users can continue critical actions without compromising security, while still enforcing verification once systems reconnect.
Performance, Scalability, and Reliability at Peak Load
Authentication endpoints are among the most performance-sensitive components of any system. A user authentication API must handle traffic spikes gracefully, especially during onboarding surges or promotional events.
Rate limiting, horizontal scaling, and built-in failover mechanisms protect systems from denial-of-service risks and ensure consistent availability. Stateless token-based designs, combined with intelligent caching, help maintain low latency even at global scale.
How Microblink Approaches API User Authentication Differently
Microblink extends traditional authentication APIs with a comprehensive identity verification platform designed for modern fraud threats. Instead of relying solely on credentials or tokens, Microblink enables applications to verify real people using government-issued IDs, face biometrics, and AI-driven fraud detection.
This approach allows businesses to authenticate users securely anywhere in the world, adapt verification flows based on real-time risk, and maintain compliance with KYC and AML regulations. For engineering teams, Microblink’s APIs integrate cleanly into existing systems while reducing fraud, false positives, and user drop-off during onboarding.
Choosing the Right User Authentication API
Selecting a user authentication API is no longer just a technical decision. It directly impacts security posture, regulatory compliance, and customer experience. Teams should look for solutions that combine strong authentication standards with identity verification, adaptive risk management, and developer-friendly integration.
As fraud techniques continue to evolve, the most effective authentication APIs will be those designed not just to verify access, but to verify identity itself. Get in touch to learn more about how Microblink can help.