How Do You Prevent SQL Injection Attacks?

In financial services, trust hinges on security. Customer onboarding platforms, identity verification APIs, and payment gateways must not only deliver seamless user experiences—they must also be airtight against threats like SQL injection (SQLi). While this vulnerability has existed for decades, it remains one of the most exploited, especially in legacy systems that still power critical financial operations.
So how do you prevent SQL injection attacks in modern financial environments without sacrificing performance or user experience?
Let’s dive into best practices, practical solutions, and overlooked opportunities that help software engineers and solution architects secure data and stay compliant while keeping friction low.
What Is SQL Injection and Why Does It Still Matter?
SQL injection is a code injection technique where attackers manipulate backend SQL queries through unsanitized input fields. This can allow them to bypass authentication, exfiltrate sensitive customer data, or even take full control of a database.
Despite increased awareness, SQLi remains a top vulnerability because it exploits weaknesses in input handling especially in complex systems or older codebases. According to the OWASP Top 10, injection flaws are still among the most common and severe security risks facing applications today.
Core SQL Injection Prevention Techniques
Preventing SQL injection starts with implementing foundational security controls. Here’s what every compliance-aware engineer should have in place:
1. Use Parameterized Queries and Prepared Statements
Avoid dynamic SQL queries that directly concatenate user input. Instead, always use parameterized queries or prepared statements provided by your framework or database layer (e.g., PDO in PHP, pg in Node.js, or PreparedStatement in Java).
Not sure which parameterized approach to use for identity APIs? Stick with your language’s native ORM or query builder (e.g., SQLAlchemy, Hibernate) and confirm it binds variables securely under the hood.
2. Implement Strong Input Validation
Validate user input for type, length, format, and range. For example:
- Only allow numeric characters for fields like Social Security Numbers.
- Block unexpected special characters in text inputs.
- Reject requests that deviate from expected patterns.
Client-side checks are helpful for user experience, but never skip server-side validation, which is critical for actual protection.
3. Use Stored Procedures Carefully
Stored procedures can reduce SQL injection risk, but they must be written defensively. Avoid dynamic SQL inside stored procedures unless you also validate inputs and use parameterization.
Security Infrastructure & Access Controls
4. Enforce Least Privilege on Database Accounts
SQL injection attacks are less damaging when the affected database account has minimal permissions. Ensure application-level accounts can only:
- Read/write from specific tables they require
- Never perform administrative operations like DROP, ALTER, or EXEC
Use role-based access controls to separate duties between services and environments (e.g., staging vs. production).
5. Deploy a Web Application Firewall (WAF)
Modern WAFs can detect and block common SQL injection patterns before they even reach your backend. While WAFs are not a silver bullet, they’re a strong second line of defense and helpful for:
- Catching known attack signatures
- Mitigating zero-day vulnerabilities during patch delays
- Logging attack attempts for audit trails
Going Beyond Basics: Detection, Monitoring & Modernization
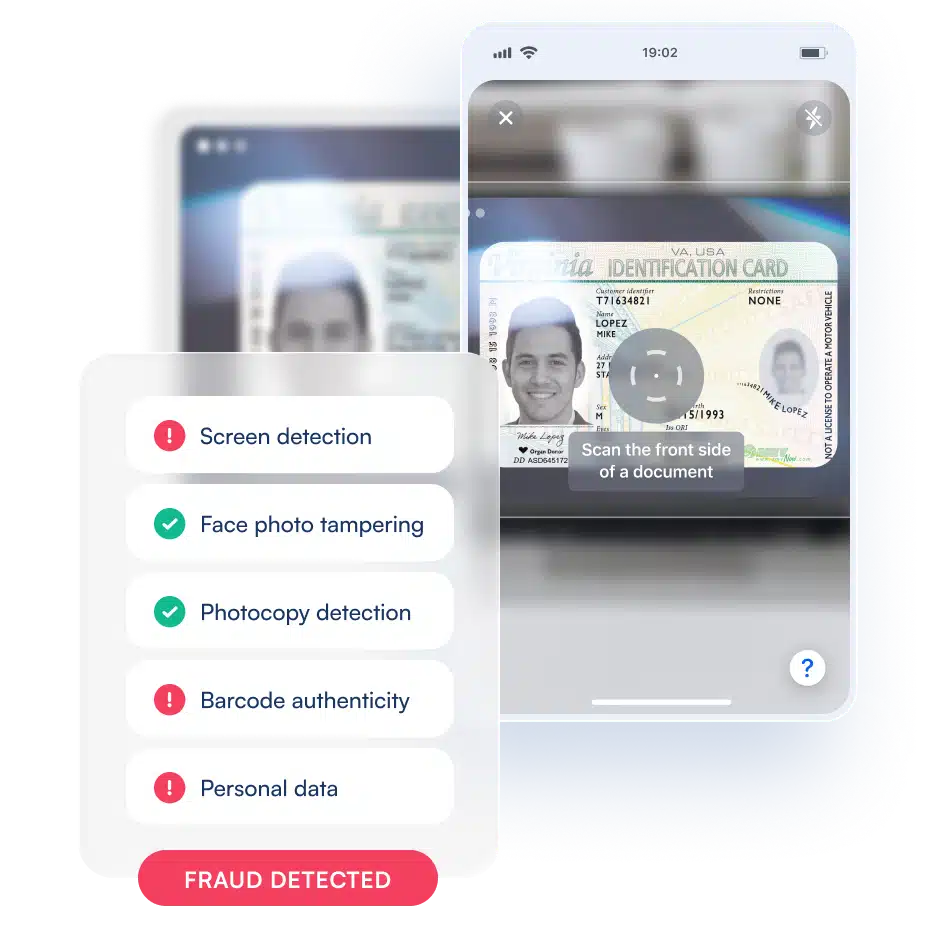
6. Implement Real-Time Monitoring and Alerts
Don’t just block attacks, detect and stop them before they happen. Use real-time monitoring tools and anomaly detection to:
- Flag abnormal query volumes or request patterns
- Trigger alerts on suspicious login attempts
- Feed data into fraud detection workflows
Behavioral analysis engines (like those used by Microblink) can be adapted to identify anomalous backend behavior linked to injection attempts.
7. Modernize Legacy Systems Without Breaking Them
Many financial institutions run legacy systems that weren’t built with SQL injection protection in mind. Upgrading those systems takes time and carries risk. But it’s possible to:
- Use middleware APIs to intercept and sanitize inputs before they hit legacy databases
- Gradually migrate to modern, secure services using compatibility bridges
- Prioritize rewrites for services that handle the most sensitive data (e.g., KYC, payments)
Balancing Security With Seamless Onboarding
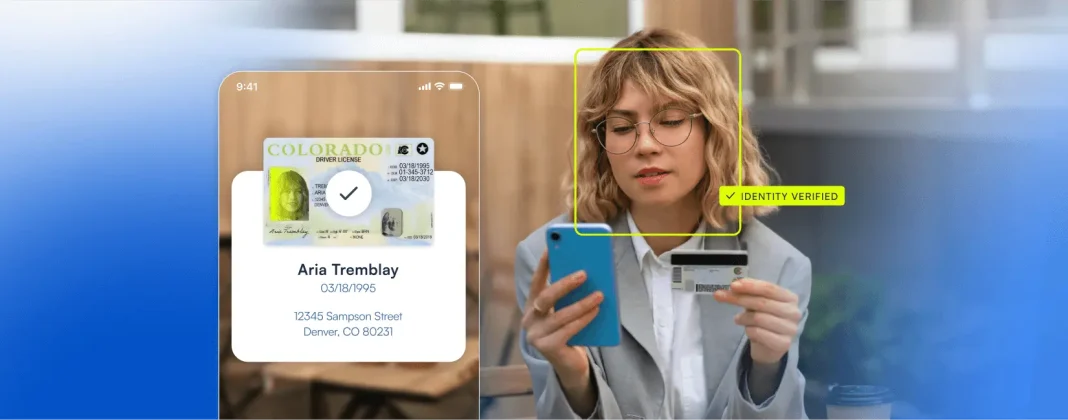
How do you secure customer databases without slowing down onboarding? The key is designing workflows where security measures are invisible to the end user but robust under the hood.
For example:
- Validate inputs client-side and server-side simultaneously
- Use asynchronous verification flows where possible
- Offload early fraud screening to background processes that don’t block onboarding
Proving Compliance: Showing Regulators You’re Protected
Regulatory bodies like the OCC, CFPB, and the SEC are increasingly scrutinizing how financial institutions protect customer data especially with emerging threats like AI-generated synthetic identities. SQL injection attacks may feel “old-school,” but that makes them all the more embarrassing if exploited.
To prove you’re covered:
- Maintain documentation of your secure coding policies
- Keep an audit trail of database activity and attack attempts
- Perform regular penetration tests and share results with compliance teams
Tools and Technologies That Help
Here are a few technologies and practices that can support your SQL injection prevention strategy:
- Static Application Security Testing (SAST) tools like SonarQube or Checkmarx to catch SQLi flaws early in the dev pipeline
- Dynamic Application Security Testing (DAST) for runtime vulnerability scanning
- ORMs and query builders that enforce parameterization
- WAFs with machine learning capabilities for evolving threat detection
- Anomaly detection APIs for real-time backend behavior monitoring
Conclusion: Prevention Is Cheaper Than Remediation
The cost of a SQL injection breach isn’t just about the technical cleanup—it’s about lost trust, fines, and potential loss of banking partnerships.
By combining secure coding practices, layered infrastructure, and real-time detection tools, you can build a resilient system that protects customer data—without sacrificing agility.