Model Context Protocol: Build Better AI Identity Verification Systems

As identity verification systems face increasingly sophisticated threats, from synthetic identities to real-time deepfakes, traditional AI models are hitting their limits. Accuracy alone is no longer enough. Context, consistency, and system-level intelligence now determine whether verification workflows scale securely or quietly fail.
This is where the Model Context Protocol (MCP) enters the picture.
Originally positioned as an open standard for connecting AI models with external data sources and tools, MCP is quickly becoming relevant for identity verification teams who need better signal quality, lower false positives, and tighter integration across fragmented systems.
This article explains what MCP is, how it improves identity verification performance, and what engineering teams should consider when deploying MCP-enabled verification systems in regulated environments.
What Is a Model Context Protocol (MCP)?
A model context protocol defines a standardized way for AI models to access, interpret, and act on contextual information from external systems, services, and data sources.
Instead of embedding logic and integrations directly into individual models, MCP acts as a context layer that supplies structured, governed inputs such as:
- Document metadata and verification state
- Device, session, and behavioral signals
- Risk scores and historical identity signals
- Regulatory or policy constraints
- Tool outputs from fraud engines, biometric systems, or databases
In practice, MCP reduces the need for brittle, point-to-point integrations by replacing custom connectors with a consistent interface between models and the systems they depend on.
For engineering teams, this means faster integration, clearer data contracts, and fewer production surprises.
Why MCP Matters for Identity Verification Systems
Identity verification is not a single model problem. It’s a system orchestration problem.
Most modern verification stacks include:
- OCR and document classification models
- Face matching and liveness detection
- Fraud and anomaly detection engines
- Rule-based compliance checks
- Risk scoring and decision logic
Without a shared context layer, these components operate in partial isolation. MCP helps unify them.
Key Benefits of MCP in Identity Verification
- Higher accuracy through richer, structured context
- Lower false positives by correlating signals across models
- Better fraud resistance against synthetic and AI-generated attacks
- Reduced onboarding friction through smarter, context-aware decisions
- Cleaner system architecture with fewer custom integrations
In short, MCP allows models to reason about identity events as part of a continuous process, not a series of disconnected checks.
How MCP Improves Accuracy and Fraud Detection
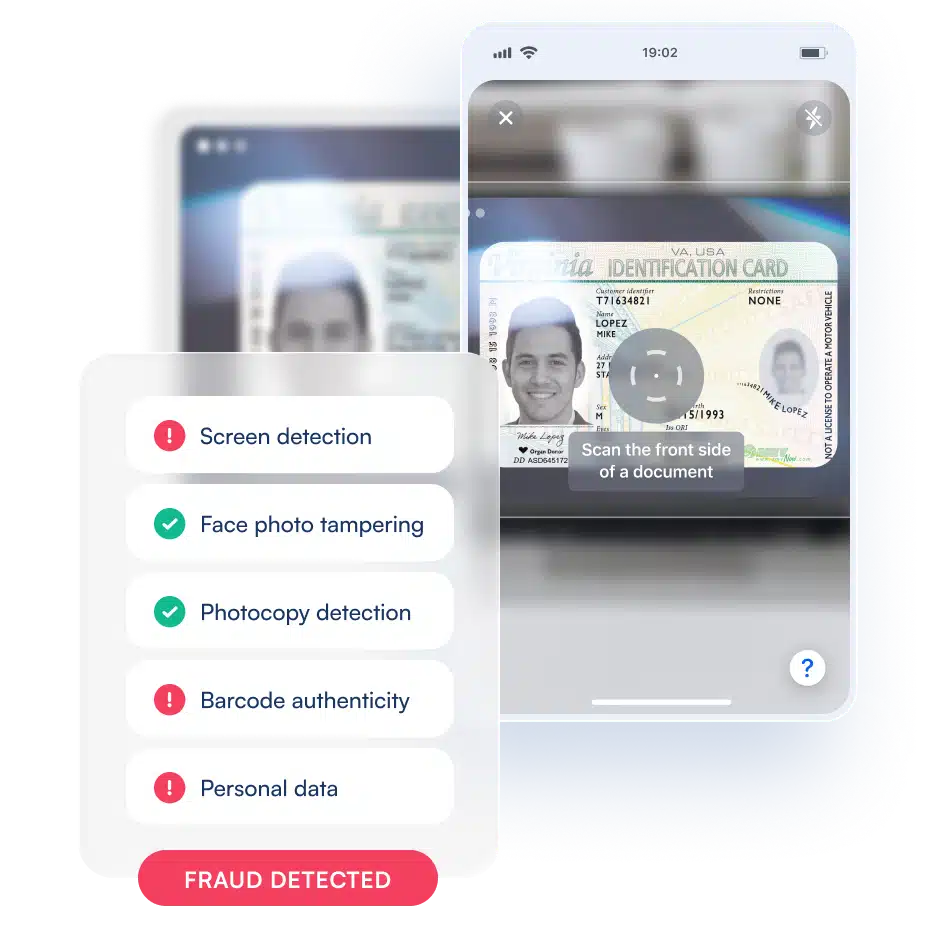
1. Synthetic Identity Detection
Synthetic identities often pass individual checks but fail at the system level.
With MCP, verification models can:
- Compare document signals against behavioral and historical context
- Detect inconsistencies across sessions and channels
- Factor in risk indicators from external fraud tools in real time
Instead of asking “Does this document look real?”, MCP-enabled systems ask “Does this identity behave consistently over time and across systems?”
That shift dramatically improves detection rates.
2. Deepfake and Biometric Attack Resistance
Deepfakes degrade isolated trust signals such as face matching or voice authentication.
MCP helps by:
- Combining biometric outputs with environmental and temporal context
- Flagging anomalies in model confidence patterns
- Coordinating liveness checks with device and session intelligence
When biometric models understand how and where they are being used, not just what they see, spoofing becomes harder to scale.
3. Reduced False Positives Without Lowering Security
A common tradeoff in identity verification is security versus user experience.
MCP reduces this tradeoff by:
- Allowing dynamic risk thresholds based on context
- Preventing redundant checks when prior verification signals are strong
- Supporting step-up verification only when risk indicators align
The result is faster onboarding for legitimate users and more friction for attackers, without blunt, one-size-fits-all rules.
Integrating MCP with Existing Identity Verification Systems
One of MCP’s core advantages is that it’s designed to work with existing systems, not replace them.
What Integration Typically Looks Like
- MCP acts as a broker between models and external tools
- Existing OCR, biometric, and fraud systems continue operating
- Context is passed via standardized schemas and APIs
- Models consume only the signals they are authorized to access
For engineering teams dealing with legacy stacks, this reduces refactoring risk while improving system intelligence incrementally.
How to Evaluate MCP-Enabled Verification Solutions
When benchmarking MCP-enabled identity verification platforms, engineering leaders should focus on system-level outcomes, not just model accuracy.
Key Evaluation Criteria
Performance
- End-to-end latency impact
- Context resolution time
- Throughput under peak load
Accuracy
- Reduction in false positives
- Improvement in synthetic identity detection
- Consistency across channels and sessions
Security and Compliance
- Access control enforcement
- Audit logging and traceability
- Alignment with KYC, AML, and data protection requirements
Operational Complexity
- Integration effort
- Observability and debugging
- Maintainability over time
MCP should simplify your architecture, not add another opaque layer.
How Microblink Supports MCP-Driven Identity Verification
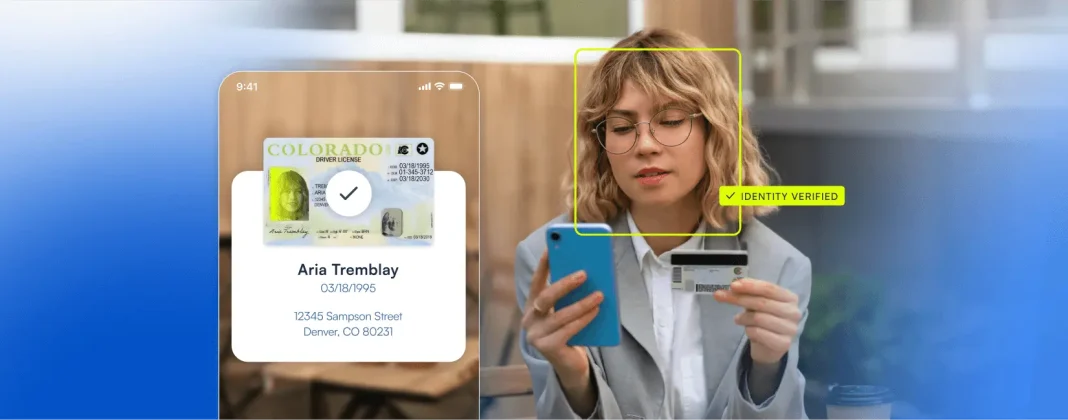
Microblink’s identity verification platform is built to support context-rich, AI-driven decisioning at scale.
By combining document verification, biometrics, fraud detection, and orchestration into a unified platform, Microblink enables MCP-style context sharing that:
- Improves fraud detection accuracy
- Reduces false positives and onboarding dropoff
- Integrates cleanly with existing systems
- Meets regulatory requirements across global markets
For engineering teams facing rising fraud complexity and performance pressure, MCP-enabled verification isn’t just an optimization. It’s becoming a necessity.
As identity threats evolve, verification systems must evolve from isolated models to context-aware architectures.
Model Context Protocols offer a practical path forward. Not by replacing existing tools, but by connecting them intelligently.
For teams building identity verification systems that need to scale securely, perform reliably, and adapt quickly, MCP is no longer optional background theory. It’s an architectural advantage.